IT & CYBERSECURITY INSIGHTS
- by Epoch Team
- Posted on May 22, 2026
Today’s SMBs need more than basic monitoring and antivirus tools. The best managed security service provider (MSSP)...
- by Epoch Team
- Posted on May 12, 2026
For a long time, businesses viewed IT support and cybersecurity as two separate things.
- by Epoch Team
- Posted on April 30, 2026
Managed IT services have become essential infrastructure for small and mid-sized businesses (SMBs) that need...
- by Epoch Team
- Posted on April 23, 2026
Why In-House IT Fails in Small Businesses The real costs, risks, and when it’s time to switch
- by Epoch Team
- Posted on March 31, 2026
Back in 2024, we published a blog outlining the key components of a successful technology plan. At the time, it...
- by Epoch Team
- Posted on January 30, 2026
Posted under:
Security
- by Epoch Team
- Posted on December 5, 2025
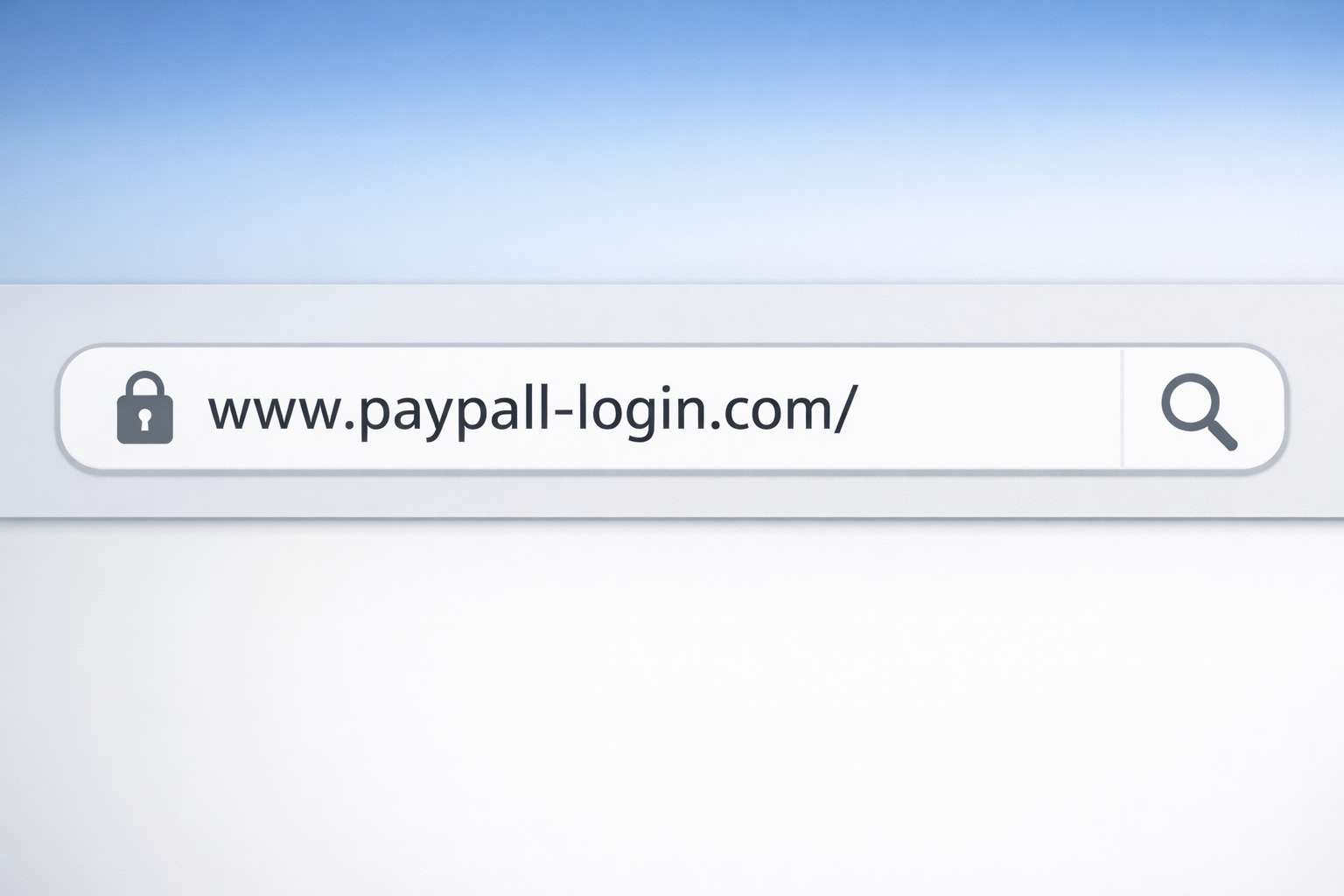
In recent weeks, our team has responded to a growing number of incidents involving a new social-engineering tactic...
Posted under:
AI
- by Epoch Team
- Posted on August 11, 2025
AI tools are everywhere, but many businesses are using them without knowing what’s under the hood. The wrong platform...